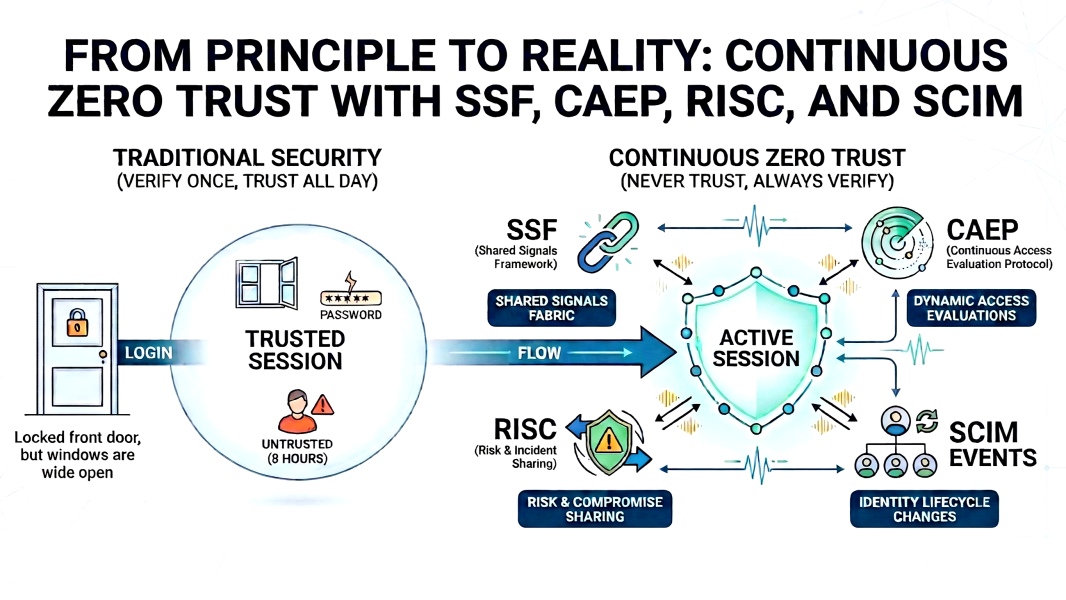
“Never trust, always verify” sounds right. But most environments verify once, at login, and then trust for the next eight hours.
That is not Zero Trust. That is a locked front door with every window wide open.
The missing piece has always been continuous verification. Not just at the moment of authentication, but throughout the entire session. The moment a device falls out of compliance, the moment credentials are compromised, the moment an employee is terminated, every active session should know immediately.
These four standards make that possible. They are not the same thing. They do not do the same job. But together they form the signaling layer that Zero Trust has always needed.
A remote employee is terminated. The decision is instant. But they are still logged into your code repository, your internal tools, and your cloud environment. No badge to revoke, no laptop to collect at the door. The only thing standing between them and your systems is how fast your identity stack can react.
The same gap exists when a device falls out of compliance mid-session, or when credentials are found in a breach dataset at 2 AM. Something critical changes, but your active sessions have no way of knowing until they naturally expire.
Four standards are specifically built to close this gap: SSF, CAEP, RISC, and SCIM Events. They are frequently confused with one another, but here is how they actually fit together to enable continuous security.
SSF: The Missing Communication Channel
Your endpoint management tool, your identity provider (IdP), and your SaaS applications all hold pieces of the security picture. Historically, they could not share those pieces in real time without fragile, custom-built, point-to-point integrations.
The Shared Signals Framework (SSF) solves this. Maintained by the OpenID Foundation, it defines a standard transport layer and a common message format, Security Event Tokens (SETs), allowing any security system to securely push real-time signals to any other.
SSF is not an alert. It is the shared language that makes alerts actionable across your entire stack. CAEP and RISC both run on top of it.
CAEP: Is This Session Safe Right Now?
The Continuous Access Evaluation Profile (CAEP) focuses on active sessions. Traditional access evaluation happens once, at login. CAEP shifts this to a continuous model. When conditions change mid-session, a CAEP event fires over SSF, allowing applications to respond instantly.
What triggers a CAEP event:
Emergency termination: The moment access is revoked centrally, a session-revoked event propagates to every active session simultaneously. Code repository, cloud console, internal tools, all of it, within seconds.
Device posture change: An endpoint drops out of compliance mid-session. Endpoint protection is disabled, or required patches are missing. CAEP signals the change so applications can restrict access before the device becomes a liability.
Impossible travel: A session authenticated from one location, and minutes later a login attempt from a geographically impossible second location. CAEP signals the anomaly across all active sessions.
Network context change: A session that started on a trusted corporate network suddenly appears on an untrusted IP. The shift in context is signaled and applications enforce policy accordingly.
Applications receiving CAEP events decide independently how to respond: full session revocation, step-up authentication, read-only access, or log and monitor. CAEP does not dictate the response. It ensures every application has the information to make that call in real time.
RISC: The Account Itself Is Compromised
The Risk Incident Sharing and Coordination (RISC) profile also runs over SSF, but operates at a different scope. Where CAEP watches the active session, RISC watches the account.
A CAEP event says, “Something changed about this session right now.” A RISC event says, “This account’s integrity is entirely compromised.” When credentials show up in a breach dataset, that is a RISC event. When behavioral analysis detects patterns consistent with an account takeover, that is a RISC event. The response is account-wide: suspend access, force a full credential reset, and notify security teams across every connected system, all triggered by a single signal.
RISC also enables cross-organization signal sharing. If a federated service detects a compromise involving one of your users, RISC is how that information reaches you before the attacker has a chance to move laterally into your environment.
SCIM Events: Identity Lifecycle Without the Lag
Standard SCIM handles provisioning and deprovisioning. It creates accounts when someone joins, and removes them when someone leaves. The limitation has always been that it runs on a schedule. Sync jobs execute on intervals, sometimes every few hours, sometimes nightly.
SCIM Events replaces that polling model with real-time push notifications for identity lifecycle changes. Unlike SSF, it operates independently within the SCIM protocol itself.
Back to the termination scenario: SCIM Events fires the moment the HR or IT record is updated. Every connected system receives the deprovisioning signal immediately. There is no residual access window waiting for the next sync cycle. The same logic applies to role changes. When someone moves to a different team, their access profile updates across every application in real time rather than drifting until the next scheduled reconciliation.
For organizations with regulatory requirements around access timelines, or high volumes of contractors, the gap between scheduled sync and real-time events is the gap between meeting compliance requirements and explaining why a terminated employee had access for six hours after the decision was made.
How They Work Together
SSF is the infrastructure CAEP and RISC run on. SCIM Events operates on its own track, handling the lifecycle layer. Together they cover the full identity security surface.
Here is what a coordinated response looks like. An endpoint security tool detects malware on a device. It sends a CAEP signal via SSF to the identity provider. The identity provider broadcasts that signal to every application with an active session for that user. All sessions are revoked within seconds. If the threat analysis confirms the account was compromised, a RISC event suspends it across all connected systems. Separately, SCIM Events ensures any provisioning or access changes tied to that account propagate immediately rather than waiting for the next sync.
The attacker’s window, the gap between something going wrong and access actually being gone, collapses from hours to seconds.
Why This Matters Now
Zero Trust as a principle has always demanded continuous verification. The practical limitation has been that verification only happened at login. You cannot continuously verify if your systems cannot continuously share signals.
SSF, CAEP, RISC, and SCIM Events are the machinery that makes continuous verification real. The major identity providers and security vendors are actively implementing these standards and demonstrating interoperability across products. This is no longer a future roadmap item.
The question for most identity teams is not whether these standards matter. It is whether their current architecture is positioned to take advantage of them, or whether they are still relying on session timers and nightly sync jobs to manage decisions that deserve a real-time response.
Where does your organization sit on this? Still in evaluation mode, or actively implementing? Would love to hear what you are seeing in the field.