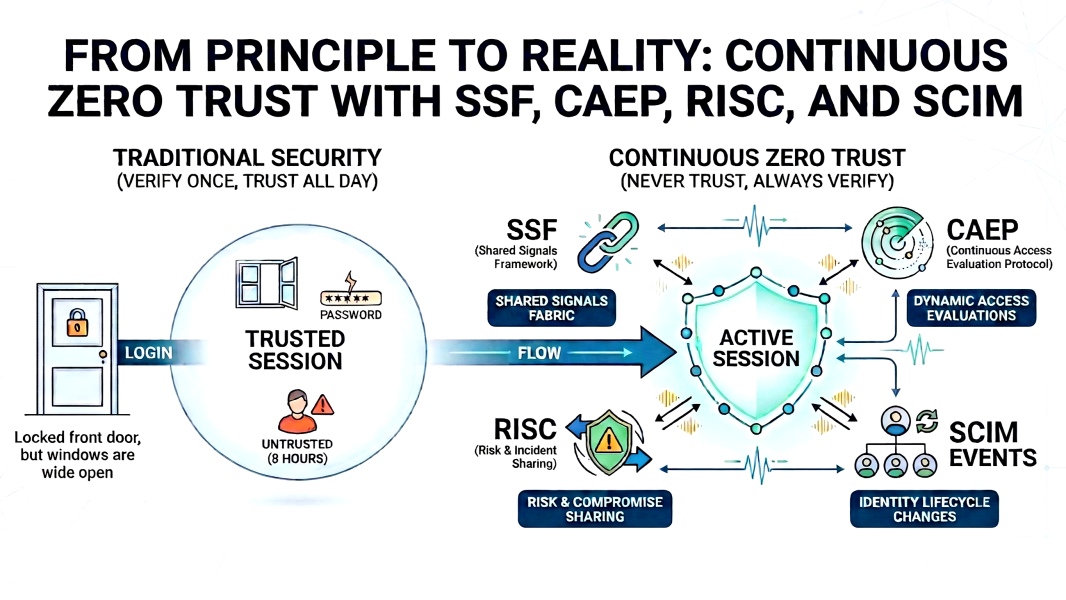
SSF, CAEP, RISC, and SCIM Events: the standards turning Zero Trust from a principle into a reality
A practical breakdown of how SSF, CAEP, RISC, and SCIM Events work together to close the gap between Zero Trust as a principle and Zero Trust as a functioning architecture.